
Critical Flaw Found in PGP and S/MIME Email Clients Like Apple Mail
Electronic Frontier Foundation (EFF) has said it has confirmed a set of vulnerabilities that have the potential to reveal the contents of email previously thought to be encrypted with PGP.
According to a blog post from the foundation, the security flaws that have been discovered could potentially leak the contents of the encrypted messages you send and receive via email when signed with PGP or S/MIME encryption methods.
The flaws, some of which have existed for more than a decade, are part of a series of vulnerabilities dubbed “Efail.” The vulnerabilities allow attackers to exfiltrate e-mail plaintexts by embedding the previously obtained cipher text into unviewable parts of an e-mail and combining it with HTML coding.
From the researchers:
The EFAIL attacks exploit vulnerabilities in the OpenPGP and S/MIME standards to reveal the plaintext of encrypted emails. In a nutshell, EFAIL abuses active content of HTML emails, for example externally loaded images or styles, to exfiltrate plaintext through requested URLs. To create these exfiltration channels, the attacker first needs access to the encrypted emails, for example, by eavesdropping on network traffic, compromising email accounts, email servers, backup systems or client computers. The emails could even have been collected years ago.
The attacker changes an encrypted email in a particular way and sends this changed encrypted email to the victim. The victim’s email client decrypts the email and loads any external content, thus exfiltrating the plaintext to the attacker.
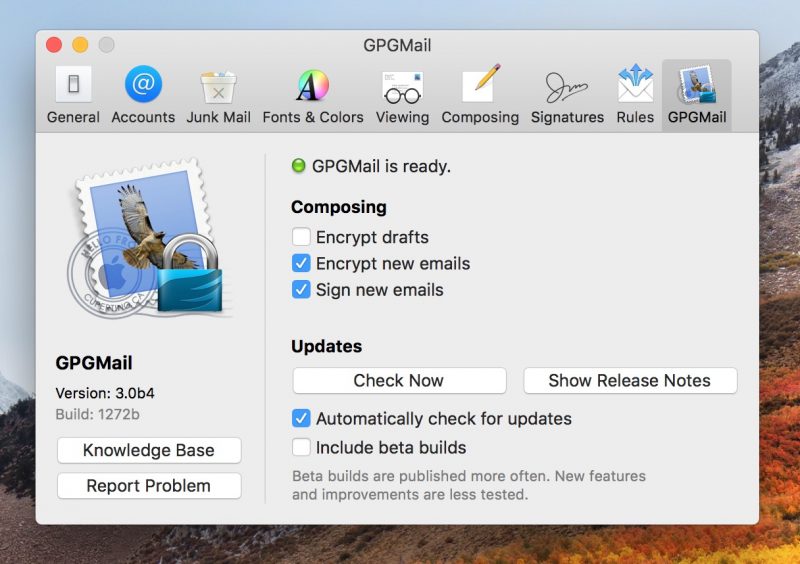
Right now there is no fix for the flaw, but there are steps PGP users can take to mitigate the risks. The Electronic Frontier Foundation advises to immediately disable all email tools that automatically decrypt PGP. A website has also been set up that advises PGP users to disable HTML renderings in emails sent via PGP as that will close the most prominent way of taking advantage of the vulnerability.
“Our advice, which mirrors that of the researchers, is to immediately disable and/or uninstall tools that automatically decrypt PGP-encrypted email,” EFF said.
“Until the flaws described in the paper are more widely understood and fixed, users should arrange for the use of alternative end-to-end secure channels, such as Signal, and temporarily stop sending and especially reading PGP-encrypted email.”
PGP, which is used to scramble the content of sensitive messages and believed to be one of the most secure methods of protecting private email communications, was once used by National Security Agency whistleblower Edward Snowden to contact journalists.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!

