
Security Researchers Discover Another iOS 6.1 Passcode Flaw [Video]
Vulnerability Lab CEO Benjamin Kunz Mejri (via Ars Technica) has today shown another way to get around the already flawed passcode lock. He outlined the vulnerability as possibly a more serious flaw than the first report highlighted.
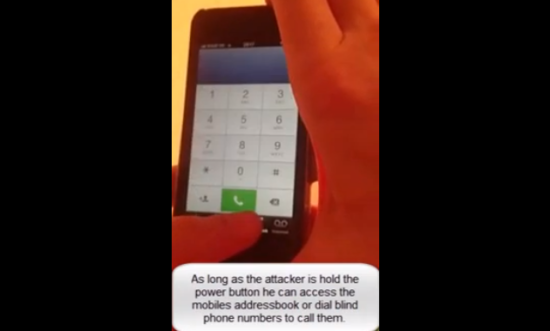
Although it seems to be similar to what we have already seen and what Apple is reported to be aware of, the new bug is slightly different. Both start out in a similar way: users need to initiate of the Emergency Call function and then put the device on standby.
The difference between the first exploit and this one is that in the case of the new one the hacker can make the iPhone screen go black and plug the device into a computer using the USB cable. This gives access to the user’s data without even the need to know the owner’s passcode.
“The vulnerability is located in the main login module of the mobile iOS device (iPhone or iPad) when processing to use the screenshot function in combination with the emergency call and power (standby) button. The vulnerability allows the local attacker to bypass the code lock in iTunes and via USB when a black screen bug occurs,” Mejri wrote. “The vulnerability can be exploited by local attackers with physical device access without privileged iOS account or required user interaction. Successful exploitation of the vulnerability results in unauthorized device access and information disclosure.”

As we previously pointed out when the first lockscreen flaw hit the blogosphere, Apple replied by acknowledging the issue. While everybody expected the company to patch the security issue with iOS 6.1.2, Apple fixed only the Exchange bug, and released iOS 6.1.3 beta 2 a couple days later containing the fix for the first exploit of the passcode security. The public version of the software update will likely be released in the near future.
Want to see more of our stories on Google?

P.S. Want to keep this site truly independent? Support us by buying us a beer, treating us to a coffee, or shopping through Amazon here. Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent Canadian media!


Way to go exposing your contact names in the video demo
An interesting flaw I discovered. Not sure if it’s IPhone or Rogers.
Recently upgraded my wifes phone from 3gs to 4s. I took the Simcard from the 3 and placed it into the 4. I have a Lumia 920 both on same account. The 4 was unable to call the Lumina, message received was “you have a call that has been blocked”…and straight to voicemail. No ringtone. After calling Rogers, Apple, Nokia all stated nothing wrong. Called Rogers again which after escalating to network support….suggested I do a factory reset on the Lumina. I didn’t do that pain in the ssss process.
I went back to the 3 and settings (still use it as a wireless device at home), saw the phone number was still in settings. I removed the number and replaced it with zeros…..now the 4 can call my 920.
Brighter minds than me can hopefully explain what transpired as I’d like to know what occurred. I’d appreciate it a great deal. Thanks in advance.
dualissue